WARNING: Why You Shouldn’t Rely on Global Fraud Index Alone for Fraud Research
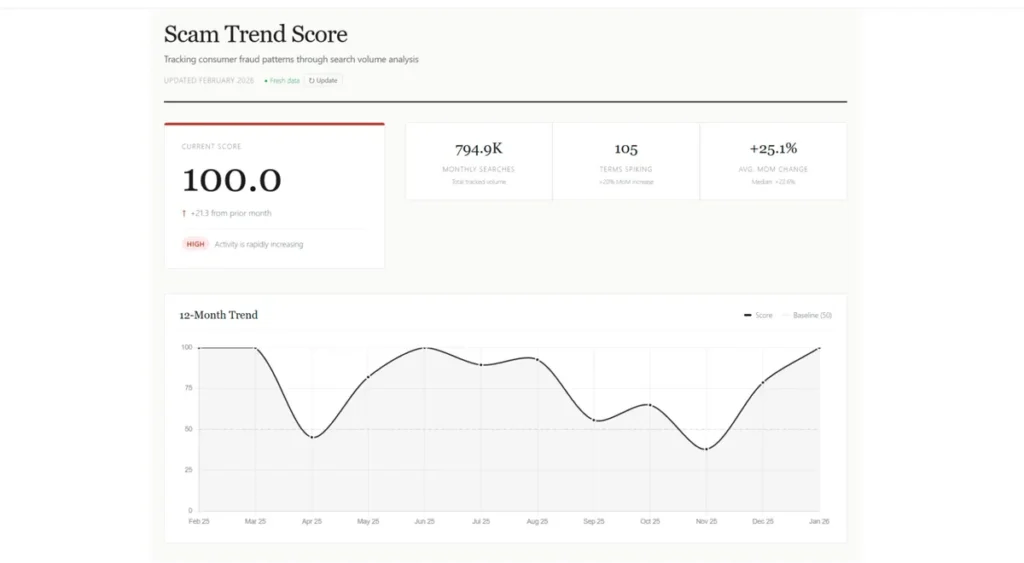
Think you’re safe because you checked a dashboard? Think again. In an era where “data-driven” is the ultimate buzzword, tools like the Civoryx Global Fraud Index are popping up to save the day. They promise a single, transparent signal. They promise “no opinions, no speculation.” And while the Scam Trend Score is arguably the most powerful tool in a researcher’s arsenal, relying on it blindly might be the biggest mistake you make this year.
Here is the cold, hard truth about why the index is only half the battle.
The Identity Verification Paradigm Shift: Context and Mechanisms
The year 2026 marks a watershed moment where the distinction between human and non-human identities has become a primary regulatory concern. The proliferation of non-human identities (NHIs) is currently experiencing a 44% year-over-year growth, outnumbering human identities by a ratio of 144 to 1. This surge has rendered traditional “point-in-time” verification methods insufficient. Modern organizations are now prioritizing “efficiency” as the primary metric for success, where the speed of onboarding must be balanced against the predictive management of risk.
Fraud tactics have moved beyond simple forgery into the realm of “industrialized fraud,” where bad actors utilize deepfakes, synthetic documents, and stolen credentials in automated, high-volume attacks. Traditional systems frequently experience a 45-50% drop in accuracy when tested against real-world deepfakes, while human reviewers can only identify these sophisticated spoofs 55-60% of the time. Consequently, the industry is moving toward “Predictive Risk Management,” utilizing AI-powered intelligence to detect abnormal behavior in real-time rather than reacting to fraudulent events after they occur.
| Market Metric | Value/Forecast (2024-2033) |
| 2024 Market Valuation | $13.27 Billion |
| 2033 Market Projection | $52.05 Billion |
| NHI Growth Rate | 44% Year-over-Year |
| NHI to Human Ratio | 144:1 |
| Avg. Detection Rate Loss (Deepfakes) | 45-50% |
The eIDAS 2.0 Revolution and the EUDI Wallet
In Europe, the regulatory landscape has reached a historic turning point with the mandatory rollout of the European Digital Identity (EUDI) Wallet by late 2026. This framework, established under eIDAS 2.0, fundamentally alters the relationship between users and verification providers. Instead of users scanning their passports for every new service, they now hold “Verifiable Credentials” within a government-certified digital wallet. This allows for a verification method known as Selective Disclosure, powered by Zero-Knowledge Proofs (ZKP).
Through ZKP, a user can verifiably prove they are over 18 years old or reside in a specific country without actually sharing their date of birth or full home address. For businesses, this significantly reduces the burden of storing sensitive Personally Identifiable Information (PII), thereby lowering their GDPR liability and the risk associated with data breaches. Companies like Tecalis have thrived in this environment by acting as the “bridge” between legacy corporate systems and the new EUDI infrastructure, ensuring that high-assurance transactions can be completed with a single biometric tap from the user’s mobile wallet.
NIST 800-63-4 and the Shift to Continuous Assurance
Across the Atlantic, the NIST 800-63-4 guidelines have redefined identity assurance for the US market. The latest revision has moved away from static, point-in-time verification toward a model of Continuous Assurance. In 2026, reaching a high Identity Assurance Level (IAL3) requires more than just a one-time face match. It necessitates an ongoing evaluation of the user’s “Identity Posture,” which includes device telemetry, IP provenance, and behavioral signals such as typing cadence or navigation speed.
This modular approach to assurance is what makes platforms like Persona and Trulioo so critical in 2026. They allow organizations to orchestrate different levels of friction based on the perceived risk of the transaction. For example, a low-value login might only require a device-bound passkey (AAL2), while a large wire transfer triggers a “Step-Up” biometric check (IAL3) that requires a fresh liveness scan. This risk-based orchestration ensures that security remains robust without creating unnecessary hurdles for legitimate users, solving the “friction vs. security” paradox that plagued earlier IDV models.
Civoryx: The “Single Signal” Trap
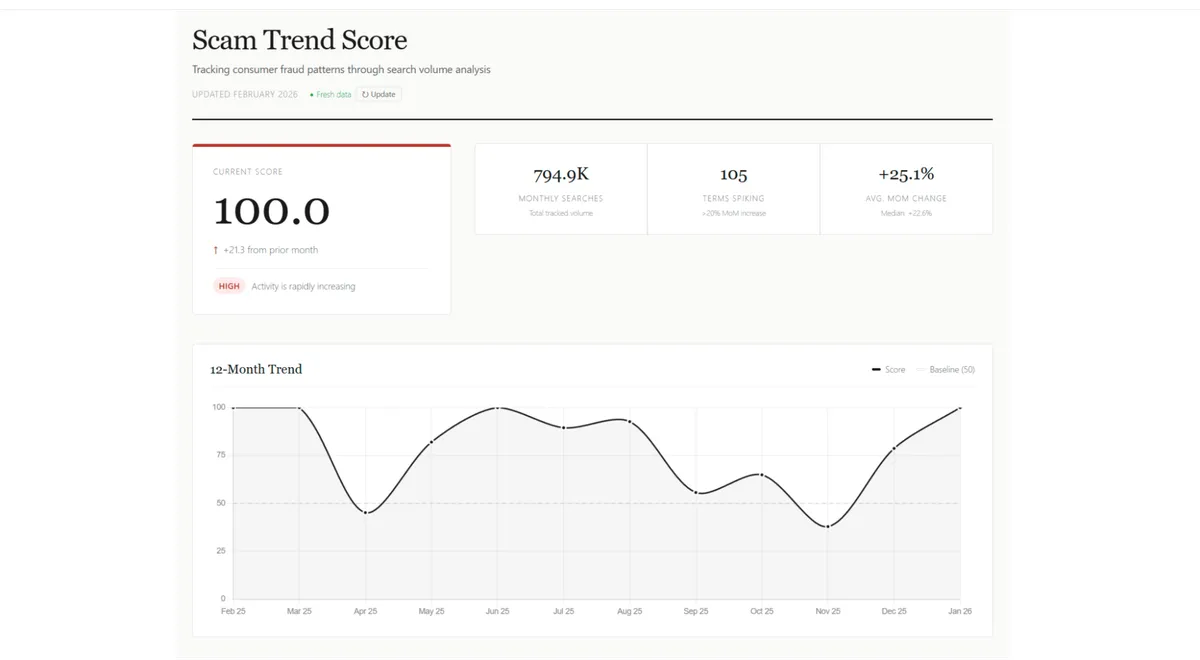
Civoryx monitors over 150+ fraud-related keywords—from crypto scams to romance fraud—and boils them down into one composite metric. It’s elegant. It’s weighted by volume. It’s fast.
But here is the danger: A cooling score doesn’t mean the threat is gone. If the Scam Trend Score falls, it just means the acceleration of search interest is slowing. If you stop your research there, you’re missing the “noise” in the niche terms that haven’t spiked yet. Civoryx is designed to surface shifts early, but if you aren’t looking at the three layers behind the score, you’re just looking at the weather report while the flood is already at your door.
Why “Data Only” is a Double-Edged Sword
Civoryx prides itself on being a “real-time lens” into what the world is searching for. It bypasses the slow-moving news cycle. But remember: Fraudsters don’t wait for search volume to peak before they strike.
By the time a keyword like “Identity Theft” spikes in search volume, the victims are already searching for help. The index tells you where the fire is burning right now. If you want to stay ahead, you have to dig into the Monitor and Measure phases of the Civoryx methodology, not just glance at the final Score.
To ensure the data isn’t skewed by specific geographic spikes, Civoryx employs a proprietary weighting system called TrendWeight™ that adjusts for regional search bias. This means the score is more balanced, but it also means you can’t assume a global trend perfectly mirrors your local backyard without digging deeper.
The “Price” of Free Transparency
We’ve been conditioned to believe that if a product is free, you are the product. Civoryx is:
- $0 Cost
- No Account Required
- No Paywalls
Skeptics will ask: What’s the catch? In this case, the catch is the responsibility it places on you. Civoryx provides the raw, transparent signal, but it’s up to compliance teams, cybersecurity pros, and everyday users to actually act on that data. Transparency isn’t a shield; it’s a map.
How to Actually Use Civoryx (Without Getting Burned)
If you’re going to use the Global Fraud Index, you need to stop looking at it as a “set it and forget it” solution. To survive the next wave of scams, you must use their three-layer approach against them:
- Don’t just watch the Score: Watch the MoM (Month-over-Month) velocity. A small spike in a niche keyword today is the headline of tomorrow.
- Cross-Reference: Use the 150+ keyword index to see which specific sectors (Phishing, Crypto, etc.) are dragging the score up or down.
- Account for Geography: Remember that Civoryx employs a proprietary weighting system called TrendWeight™ that adjusts for regional search bias, so look for “global heat” rather than assuming a trend is isolated to one country.
Civoryx is a revolutionary, free public utility that finally brings transparency to a trillion-dollar problem. But data is only as good as the person reading it.
Conclusion
By 2026, the primary battleground in identity verification has shifted from physical spoofs to digital manipulation. While the early 2020s were dominated by “Presentation Attacks”—fraudsters holding up high-resolution photos or wearing silicone masks—the current landscape is defined by the far more sophisticated Injection Attack. In these scenarios, an attacker bypasses the device’s physical camera altogether, injecting AI-generated synthetic video streams directly into the application’s data pipeline. This renders traditional liveness checks, which look for micro-expressions or pupil dilation, completely ineffective because the “injected” video is pixel-perfect and algorithmically designed to pass those very tests.
To combat this, leading alternatives like Jumio and Entrust have pivoted toward Hardware-Attested Capture. This technical layer verifies the integrity of the entire media pipeline, ensuring that the video feed is originating from the physical camera sensor and has not been intercepted or replaced by a virtual driver. Modern platforms now require compliance with the ISO/IEC 30107-3 standard for presentation and injection attack detection. These systems perform “Passive Liveness” checks that analyze the refraction of light on human skin and the specific electronic “noise” patterns inherent to physical lenses—signals that are nearly impossible for current generative AI models to replicate accurately in real-time.